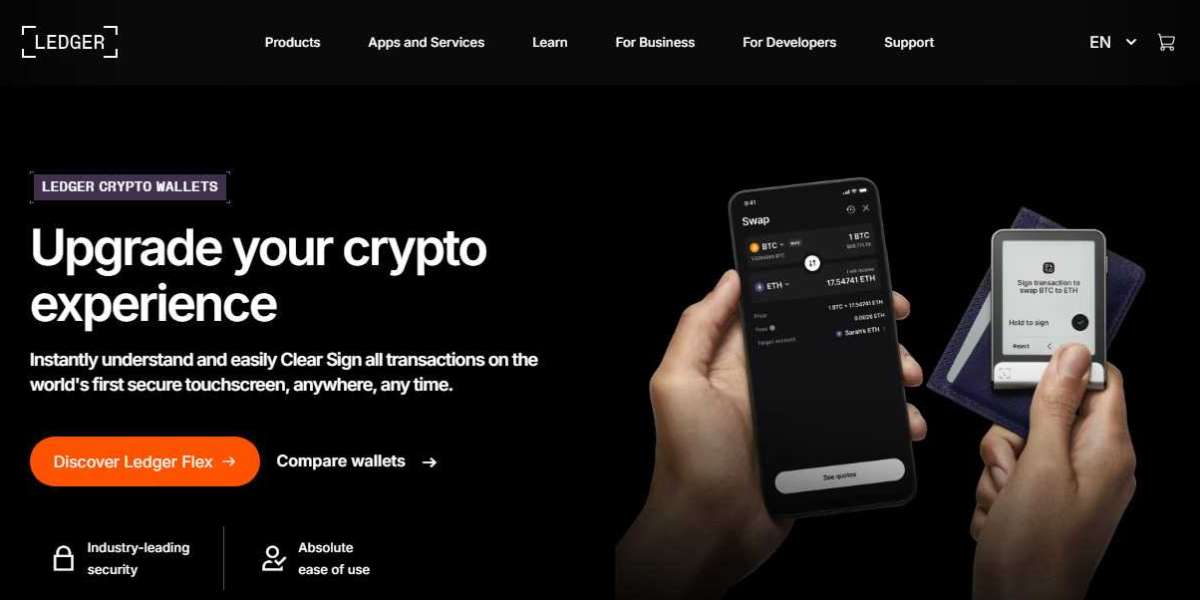
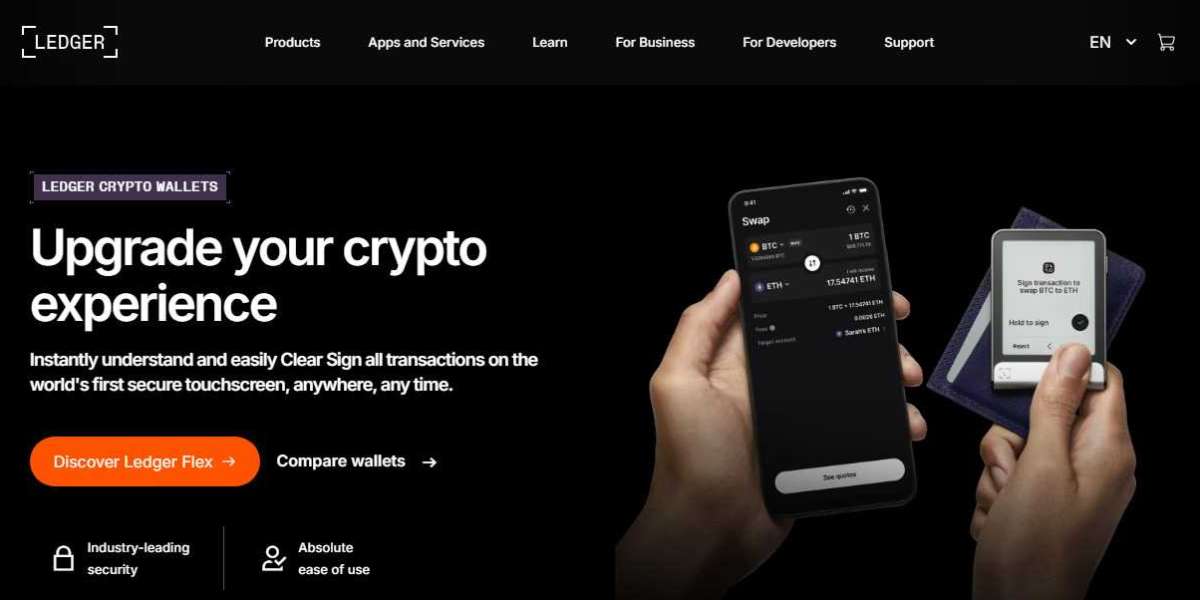
Ledger Login – Secure Access to Your Crypto Assets
Ledger login refers to the secure process of accessing your cryptocurrency accounts using a Ledger hardware wallet in combination with the official Ledger Live application. Unlike traditional online platforms that rely on usernames and passwords stored on servers, Ledger’s login system is built around hardware-based security and private key ownership. This approach ensures that only you have control over your digital assets.
What Is Ledger?
Ledger is a leading hardware wallet provider that develops secure devices designed to store cryptocurrency private keys offline. Popular devices such as the Ledger Nano S Plus and the Ledger Nano X protect digital assets from online threats like malware, phishing attacks, and hacking attempts. Ledger devices work together with Ledger Live, the official desktop and mobile application, to help users manage, send, receive, stake, and monitor crypto holdings.
Understanding Ledger Login
Unlike traditional web-based login systems, Ledger does not use a standard username and password for account access. Instead, the login process involves:
A Ledger hardware wallet device
A PIN code set during device setup
The Ledger Live application
A 24-word recovery phrase (created during initialization)
When you connect your Ledger device to Ledger Live, you unlock it using your PIN. The device then verifies and signs transactions internally without exposing your private keys to your computer or the internet. This is what makes Ledger login fundamentally different and more secure than centralized exchange logins.
How to Log In to Ledger Live
Here is a step-by-step overview of the Ledger login process:
Download Ledger Live
Install the official Ledger Live application on your desktop or mobile device from the official Ledger website.Connect Your Device
Use a USB cable (or Bluetooth for Nano X) to connect your Ledger hardware wallet.Enter Your PIN
Unlock the device by entering your secure PIN code directly on the hardware wallet.Open the Required App
Navigate to the specific cryptocurrency app (such as Bitcoin or Ethereum) on your Ledger device.Access Your Portfolio
Once unlocked and connected, Ledger Live will display your portfolio, balances, and account options.
There is no cloud-based login or password reset process. Access is entirely dependent on physical device possession and PIN authentication.
Security Features of Ledger Login
Ledger login is built around advanced security architecture designed to minimize risks. Key features include:
1. Secure Element Chip
Ledger devices use a Secure Element chip (similar to those used in passports and credit cards) to store private keys safely.
2. Offline Private Key Storage
Your private keys never leave the hardware wallet. Even if your computer is compromised, attackers cannot extract your keys.
3. PIN Protection
The PIN prevents unauthorized access to your device. After several incorrect attempts, the device resets itself.
4. Recovery Phrase Backup
During setup, users receive a 24-word recovery phrase. This phrase is the only way to restore assets if the device is lost, damaged, or reset.
5. Transaction Verification on Device
Every transaction must be physically confirmed on the device screen, preventing unauthorized transfers.
Common Ledger Login Issues
While Ledger login is designed to be secure and simple, users may occasionally encounter issues:
Incorrect PIN entry leading to device reset
Outdated Ledger Live software
USB connectivity problems
Bluetooth pairing issues (Nano X)
Phishing websites pretending to offer Ledger login pages
It is important to note that Ledger does not provide online login portals requesting recovery phrases. Any website asking for your 24-word recovery phrase is fraudulent.
Recovering Access to Ledger
If you forget your PIN or your device resets, you can restore access using your 24-word recovery phrase. Simply initialize the device again and choose the “Restore from recovery phrase” option. Enter the words in the correct order to regain full access to your crypto accounts.
If you lose both your device and recovery phrase, access to your assets cannot be restored. This highlights the importance of securely storing your recovery phrase offline in a safe location.
Best Practices for Secure Ledger Login
To maximize security when using Ledger login:
Never share your 24-word recovery phrase with anyone
Avoid taking digital photos of your recovery phrase
Always download Ledger Live from the official Ledger website
Keep your device firmware updated
Verify transaction details directly on your device screen
Beware of phishing emails claiming to be from Ledger
Why Ledger Login Is Different from Exchange Logins
Many cryptocurrency exchanges operate using traditional email-and-password systems where assets are stored on centralized servers. In contrast, Ledger login ensures you retain full custody of your private keys. This self-custody model reduces the risk of exchange hacks, frozen accounts, or third-party control.
Because Ledger is a non-custodial solution, the company itself cannot access, reset, or control your funds. Security responsibility lies entirely with the user.
Conclusion
Ledger login is not a typical web login experience. It is a secure authentication process that combines hardware protection, PIN verification, and offline private key storage to safeguard digital assets. By using devices like the Ledger Nano S Plus or Ledger Nano X alongside Ledger Live, users gain full control and ownership of their cryptocurrency holdings.